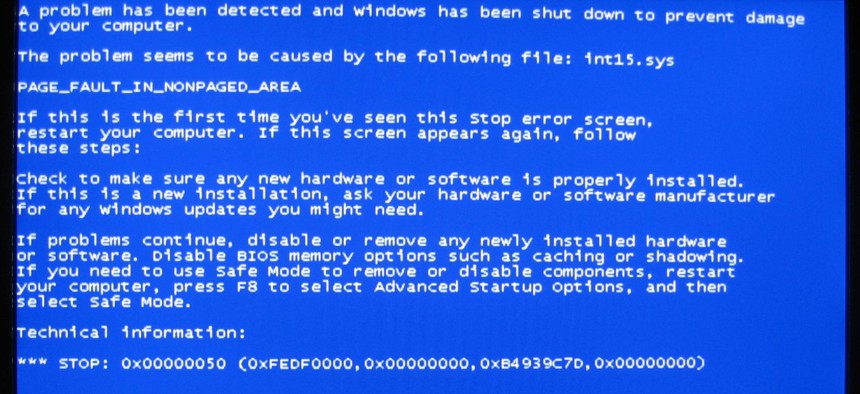
A Windows error message commonly referred to as the 'blue screen of death'. Flickr image via Bruce Guenter
The Secret Pentagon Push for Lethal Cyber Weapons
With nearly $500 million allotted, military contractors are competing for funds to develop the next big thing: computer code capable of killing.
Under a forthcoming nearly half-billion-dollar military contract, computer code capable of killing adversaries is expected to be developed and deployed if necessary, according to contractors vying for the work and former Pentagon officials.
U.S. troops would have the power to launch logic bombs, instead of traditional explosive projectiles, which essentially would direct an enemy's critical infrastructure to self-destruct.
Lethal cyber weapons have arrived.
As previously reported, an upcoming $460 million U.S. Cyber Command project will outsource to industry all command mission support activities, including “cyber fires" planning, as well as "cyberspace joint munitions" assessments.
Unlike traditional espionage malware or even the Stuxnet virus that sabotaged Iranian nuclear centrifuges, cyber fires would impact human life, according to former Defense officials and a recently released Defense Department "Law of War Manual."
The visceral response to the word "war" for anyone in uniform is that it's ugly and people get killed, said Bill Leigher, a recently retired Navy admiral with decades of warfighting experience who now runs Raytheon's government cyber solutions division.
"When I use 'cyberwar,' I'm thinking of it, in a sense of war," he said. "So, yes, war is violence."
Raytheon, Northrop Grumman and Lockheed Martin are among the major defense firms expected to compete for the CYBERCOM contract.
Pentagon Doctrine OKs Digital Arms
Going on the offensive in cyberspace, essentially means "defeating the interaction between a processor and its software" to serve a mission, Leigher said.
"Combatant commanders choose weapons that they know will further their course of action," he said.
If the commander needs to fly an aircraft over an occupied area, and wants to use malware or another cyber capability to help accomplish that goal, the officer must have confidence the cyberattack will work as expected.
"I trust it. I know how it's going to be used, and I believe that it is the best option to execute and it doesn't create more risk for the 27-year-old Air Force pilot who is flying over a defended target," Leigher described the decision-making process.
In this case, maybe the bull’s-eye would be a maintenance facility on an airfield. By launching a cyberattack, a commander could, for example, shut down the power grid of the facility, and then "you've degraded the enemy's ability to repair aircraft," Leigher said.
Digital arms designed to kill are sanctioned under Pentagon doctrine.
There is a chapter titled "Cyber Operations" in DOD's first-ever "Law of War Manual," published in June. The section reflects the department's' growing transparency surrounding cyberwarfare, national security legal experts say. Less than three years ago, most activities beyond defensive maneuvers were classified.
The manual lays out three sample actions the Pentagon deems uses of force in cyberspace: "trigger a nuclear plant meltdown; open a dam above a populated area, causing destruction; or disable air traffic control services, resulting in airplane crashes."
Same Rules for Traditional Bombs or Bullets
The Pentagon’s stated role in cyberspace is to block foreign hackers targeting domestic systems, assist U.S. combat troops overseas and defend military networks.
The U.S. armed forces “are developing tools and capabilities” necessary to carry out all three of those missions, Pentagon spokeswoman Laura Rojas told Nextgov in an email. “We do this consistent with U.S. and international law."
The law is clear that cyber operations might also kill civilians, the experts say.
Cyber strikes are allowed even if “it is certain that civilians would be killed or injured -- so long as the reasonably anticipated collateral damage isn’t excessive in relation to what you expect to gain militarily," said retired Maj. Gen. Charles J. Dunlap, executive director of Duke University's Center on Law, Ethics and National Security. "These are essentially the same rules as for attacks employing traditional bombs or bullets.”
Because nearly all military forces depend on the same networks as civilians, it is not hard to imagine a situation where a cyberattack takes innocent lives, Dunlap said.
"A piece of malware, for example, might destroy a military industrial-control system of some sort, but if not designed to self-neutralize, it might go on to do the same to a civilian system of similar design, possibly with fatal consequences to civilians," Dunlap said.
Destructive cyberattacks also risk the possibility of nonviolent collateral damage. Microsoft, as of March, was still dealing with the fallout from the spread of the Stuxnet virus. Microsoft had to issue a patch for a software flaw the U.S. and Israel allegedly used to take over the specific system running Iran's nuclear equipment. To date, there have been no reports of other infected machines reacting the same way.
Will Adversaries Follow Same Rules?
The use of lethal software aligns with 2010 comments by then-Deputy Defense Secretary William Lynn published in Foreign Affairs, stating, "As a doctrinal matter, the Pentagon has formally recognized cyberspace as a new domain of warfare.”
“What we see right now is essentially the implementation of the decision," said Tim Maurer, a cyber policy researcher at the Carnegie Endowment for International Peace.
In elaborating on the term “cyber joint munitions,” CYBERCOM spokeswoman Kara Soules told Nextgov in an email that understanding the success rate of the weapon is critical.
“‘Cyber joint munitions effectiveness’ describes that a particular cyber capability has been evaluated and its effectiveness is known against a particular target,” she said. The target is a person, place or object a commander is eyeing to neutralize, according to the associated Joint Chiefs of Staff policy.
“Cyber fires” has a broader meaning and “can be used for offensive or defensive objectives, and can be designed to create effects in and through cyberspace,” she said.
Outside the United states, other governments are hiring nongovernment organizations to build cyber munitions, too, Maurer noted. Some of them operate underground. For instance, there are hackers who sell "zero day" exploits capable of attacking systems containing undetected security vulnerabilities known only to the seller.
Black hat hackers who can sell cyber munitions to governments as well as extremist groups like ISIS thrust the world into unknown territory.
"I’m fairly confident that U.S. cyber capabilities can be very precise and targeted and tailored," Maurer said. The question, though, is whether it is possible for "less-sophisticated actors to be similarly targeted and tailored in the tools that they use.”
The discussion surrounding the firing of cyber arms hearkens back to before the days of Manhattan Project, some former military leaders say.
“It reminds me of the run-up to the strategic bombing campaigns of World War II,” said Cedric Leighton, a retired National Security Agency and Air Force intelligence director. “Just like then, the consequences of an attack using cyber munitions will not be completely foreseeable.”
CYBERCOM should be examining code warfare today, if only to be prepared: “Our military could be confronted by a tough cyber adversary at any moment," he added.




